This post results from the project “DFIR & Threat Intelligence” within the Munich Cyber Security Program (MCSP) The MCSP is a cooperation project between Champlain College and Com|Code (Germany). This project focuses on new developments in the Digital Forensics and Incident Response fields as well as performing research for clients of
Com|Code
One month into the MCSP DFIR & Threat Intelligence internship and I have learned so much already. After ironing out the project’s scope in the first couple of weeks, I have spent my time performing Open Source Intelligence (OSINT) for Com|Code clients in Germany and keeping track of major hacker groups across the globe. Multiple aspects of this project are ongoing, and admittedly will be for the entirety of the internship. Also, I am excited for the third aspect of the project, which involves a tool evaluation with Binalyze Forensics. The initialization of this evaluation is in development, but we will be providing constant updates through LinkedIn and this blog page, so stay tuned!
OSINT – A Crucial Step in Cybersecurity
Where my interest and education focuses on practical, hands-on security, I didn’t understand the true importance of research within cybersecurity. My vision of research when joining this team was keeping up-to-date with CVEs and reporting major data breaches. Then I was asked to perform my first OSINT report on a client. Thirty pages later, I discovered that there is way more publicly available data on organizations than I could have ever thought. With the right tools, all of which were available for free, I was able to identify mission-critical vulnerabilities, domains that were supposed to be private, and the internal infrastructures of the systems I was researching. What I once used to view as a formality, I now realize is perhaps the most important part of implementing a cybersecurity policy.
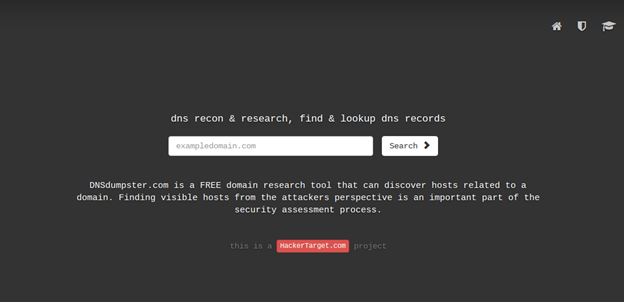
There are multiple tools that can assist an OSINT investigation into a company. On their own, the results they produce can be limited, but using them together have produced more domains and IPs than any Google search would provide. To follow my methodology when performing an OSINT report, the first tool I always turn to is DNSDumpster. It functions as a domain/IP discovery tool and there are many alternatives. However, I have found that this tool specifically has always provided accurate results.

Using this information, there are two tools that can expand on and produce even more domains and IP addresses. The first of them is called SecurityTrails. It contains a massive database of DNS records, able to provide new domains to explore by searching for IPs. This doesn’t necessarily increase the attack vector of a company, as many of the domains are not reachable and this will not produce new IP addresses.

To discover the larger attack vector, I input the domains I have discovered so far into BuiltWith. This accomplishes two different steps of the OSINT. BuiltWith will report new domains attached to the one I’m searching, which usually are currently accessible, and may be hosted on new IP addresses. This site also discovers the services, frameworks, and tools being used to host and monitor the domain and web pages within the domain. This is useful in an OSINT as it can provide insight into the services that an attacker would attempt to exploit if they are vulnerable.

Finally, with all the above information I have gathered, perhaps the most useful tool I’ve discovered (which, admittedly, appears pretty well-known) is called Shodan. By entering a domain or IP address (IP addresses are more likely to produce results), Shodan can report on open networking ports, the services/software running on that port, known vulnerabilities of those software/services, web technologies active, and an approximate geographical region where the IP is being hosted.
Threat Intelligence – Keeping Track of Ransomware
The other aspect of my internship involves staying up-to-date with major ransomware groups this year. I was asked specifically to research Hive and LockBit at different points during the past month. These two groups are important as they are the leaders in an emerging ransomware framework known as Ransomware-as-a-Service (RaaS). This approach to ransomware is “safer” for the groups. Essentially, when referring to the LockBit and Hive groups, it is more accurate to say that they are developers, programming the ransomware and providing a live help chat feature to clients. These “clients” are the attackers that actually exploit and compromise a network. Once they enter a network, they execute the ransomware essentially the same way you would open Google Chrome. The “developer” group doesn’t stop there, however, as they provide assistance to clients on how to negotiate a ransom and they will release victim data provided by the client if the victim refuses to pay the ransom.

Hive, in particular, was a fascinating group to research. Because one/some of the internal developers pledged allegiance to Russia towards the start of the Russia/Ukraine conflict, one of the members leaked private chat logs, giving insight to their organizational structure. Another research group was also able to sign up for the ransomware and shared images of the Hive dashboard, including how a client accesses the ransomware payloads and how they chat with the main group after a successful attack. Thanks to these sources, I feel like I am pretty familiar with Hive and how they operate. However, this industry is constantly evolving. To give an example, on the day that I am writing this it was discovered that there is a new version of Hive that has been out in the wild for some time, taking advantage of a new operating system and upgrading the encryption process.

LockBit is the other industry-leading RaaS and is also constantly growing and improving. On the day that I was asked to research them, they had just released LockBit 3.0 with a ground-breaking bug bounty program. Bug bounties are more common in software companies attempting to improve their products but this was the first program tied to a malicious group. Essentially, LockBit has obtained enough wealth to fund multiple prizes between $1000 and $1m for security vulnerabilities in their software, ideas on how to improve the ransomware, or even the name of the manager of LockBit. This is just one indicator of how professional LockBit appears to be, so I am constantly keeping tabs on both them and Hive as their next, extreme change could be hours away.
Follow us for more updates on this project! For further questions about Munich Cyber Security Program, or this project please feel free to contact mcsp@comcode.de
-Written by Joseph Fustolo ‘23 //Digital Forensics & Cybersecurity